
The holidays are here, and I hope everyone made it safely through Black Friday, Small Business Saturday, and Cyber Monday. Wait, safely through Cyber Monday? You probably never left the comfort of your sofa as you purchased that drone, did you? Of course, I’m talking about Internet and network security.
As a Cisco Gold Partner with a history of implementing voice, network and data center solutions, the Consolidated Communications resume is rich with experience. And while Cisco’s core business of selling more routers and switches than anyone else on earth continues, their fastest growing segment is security.
Cisco has always been known for their firewalls, specifically the ASA series, which did a great job of keeping the bad guys out. But what about expert hackers who found holes in the security stack and were still able to penetrate an organization’s network? Remember, it’s not a question of IF a company gets hacked, it’s a matter of when.
In July 2013, Cisco acquired a company called Sourcefire for $2.7 billion, which is one of the largest acquisitions in a long list companies they’ve gobbled up. (Thanksgiving pun intended) So what did this do for Cisco’s suite of security solutions? Well, simply put, it gave them a suite.
Cisco quickly went from having a great firewall product to having one of the most elite security solutions available on the market today. And while security is an incredibly complex, fast moving problem, the strategy from Cisco is simple: The Attack Continuum.
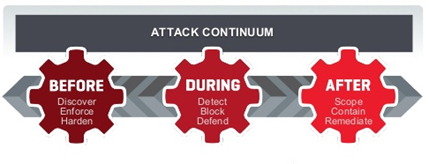
Image Source: Cisco White Paper - Addressing the Full Attack Continuum: Before, During, and After an Attack.
Before: Keep the bad guys out. Remarkably, this product suite defeats over 99% of all attacks, which is an impressive number until you consider the denominator: Millions of attacks are attempted daily.
During: What to do once the hackers are in. If you’d like some background on what happens at this step, check out Sandbox (computer security).
After: Retrospective security. Forensics and analytics are needed to identify how and where the intrusion happened, determine the threat, and prevent additional attacks.
In early 2013, the total addressable market for security products and services was at $58 billion. In December 2013, Target Corporation was hit in a well-publicized security breach and the security TAM rapidly grew to $65 billion in early 2015. Cybersecurity is estimated to cost us $400 billion per year, and that number is also growing. What’s in it for the criminals? Illegal access to locked information, identity theft, and the thrill of trolling for starters.
Fortunately, none of this has prevented my personal household from hammering our Amazon Prime account as we load up on diapers and the endless array of headband apparel available for a newborn girl. (Apparently that’s a thing.) But just as Consolidated Communications helps organizations do their part to improve their security stack, as individual consumers it’s important to be vigilant in our own online shopping experience to protect our personal information and prevent cybercriminals from putting a damper on the holidays. Here are some good tips to protect yourself while shopping online this holiday season.
About the Author

Andy Berg , Director of Sales
Andy has been in the IT industry for over 20 years and joined Consolidated Communications in 2012 as the Director of Sales, where he manages the IT services sales organization covering everything from small business to large enterprise to public sector. Throughout his career, Andy has held positions in Engineering, Architecture, Sales, and Leadership with top industry names like Verizon, eLoyalty, and Spanlink. Andy started his career with Carlson Wagonlit Travel and Prudential Insurance, where he made key contributions as a Manager and Engineer on various voice and contact center platforms.